Penetration Tester
Role details
Job location
Tech stack
Job description
The NCIA NATO Cyber Security Centre (NCSC) is responsible for planning and executing all lifecycle management activities for cyber security. In executing this responsibility, NCSC provides specialist cyber security-related services covering the spectrum of scientific, technical, acquisition, operations, maintenance, and sustainment support, throughout the lifecycle of NATO Information Communications and Technology (ICT). Within the NCSC, the Assess Branch performs comprehensive vulnerability assessments, penetration testing, security compliance audits and red teaming activities against NATO CIS components throughout their lifecycle and across the NATO CIS footprint, improving its cyber hygiene while contributing to the CIS accreditation, IT change management and cyber incident response and recovery processes. It reports on security shortfalls and provides expertise in support of the mitigation and remediation assistance process. The Section also supports exercises, software development assurance and purple teaming activities.
The Penetration Testing Section manages and conducts tailored penetration testing activities against NATO networks and systems, with the objective to assess the impact of current cyber threats, as well as, their likelihood and difficulty of exploitation, on NATO CIS, a NATO Mission or NATO's cyber defences by emulating an intermediate or advanced cyber adversary. These unique activities are performed in support of accreditation, IT change management and software development assurance throughout the lifecycle
Role Duties and Responsibilities
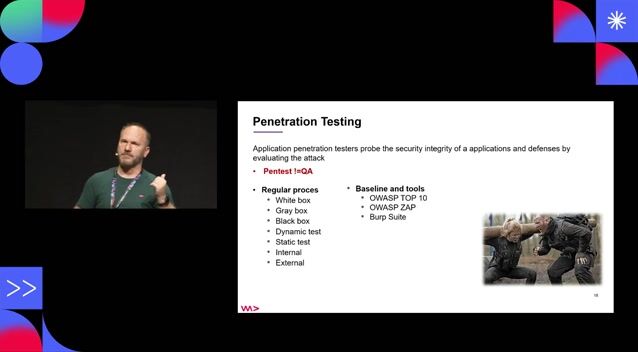
- Providing Web, infrastructure and application level penetration testing, including but not limited to COTS software and NOTS/GOTS software (NATO/Government off the Shelf), following clearly defined methodologies.
- Participating in kick-off meetings with stakeholders and technical points of contact in order to identify requirements for testing.
- Following the documented procedures and workflows outlined by the technical leads.
- Attending team meetings if required.
- Writing technical reports in fluent English, following defined templates and Reporting Tools.
- Briefing, at both executive and technical levels, on security reports and testing outcome, including at flag officer level.
- In case of new vulnerabilities detected for COTS software, following the Responsible Disclosure Process and following-up with vendors and stakeholders.
- Providing security design reviews to ensure compliance with NATO policies and directives.
- In co-ordination with the Technical Lead of the Penetration testing team, ensuring proactive collaboration and coordination with internal and external stakeholders.
- Staying abreast of technological developments relevant to the area of work.
- Performing any other duties as may be required.
Requirements
Do you have experience in Windows?, Do you have a Bachelor's degree?, * Extensive knowledge and experience (at least 3 years) in the following areas:
- Web application penetration testing
- IT infrastructure penetration testing
- Network security architecture design
- Assessing security vulnerabilities within OS, software, protocols & networks
- Researching and evaluating security products & technologies
- Knowledge in system and network administration of UNIX and Windows systems
- Use of penetration testing tools, techniques, and recognized testing methodologies
- Scripting skills in at least one of the following: Python, Go, PowerShell, shell (bash, ksh, csh)
- Technical knowledge in system and network security, authentication and security protocols, cryptography, application security, as well as, malware infection techniques and protection technologies.
- Ability to evaluate risks and formulate mitigation plans.
- Proven ability to brief at executive level on security findings, reports and testing outcome.
- Proven ability to write clear and structured technical reports including executive summary, technical findings and remediation plan for several different audiences.
Desirable Skills, Experience and Certifications
- Professional qualifications: OSCP, OSCE, OSWE, GPEN, CREST Certified Web Application Tester, GXPN, GWAPT or equivalent
- Familiarity with risk analysis methodologies.
- Prior experience of working in an international environment comprising both military and civilian elements.
- Knowledge of NATO organization, internal structure and resultant relationships.
- A thorough knowledge of one of the two NATO languages, both written and spoken, is essential and some knowledge of the other is desirable., * Bachelor of Science (BSc) degree at a nationally recognised/certified university in a technical subject with substantial Information Technology (IT) content and 3 years post-related experience. As an exception, the lack of a university degree may be compensated by the demonstration particular abilities or experience that are of interest to the NCIA; namely, at least 10 years of extensive and progressive experience in the duties related to the functions of this post., * Valid National or NATO Secret personal security clearance