Senior Cloud Security Consultant
Role details
Job location
Tech stack
Job description
All of this is built on four fundamental values that define who we are: We are Proud, We Break Barriers, We Care and No BS!
Tasks
You will be joining NVISO's Cloud Security team as a Cloud Security (Sr.) Consultant. The ideal candidate has knowledge in Azure or Microsoft 365 cloud services, with a particular focus on security.
We are aware that cloud security features and products are abundant; the following list apply to the ones of interest to us. If you have experience or feel capable of conducting only some of them (not the full list), please reach out!
Strategy and Governance
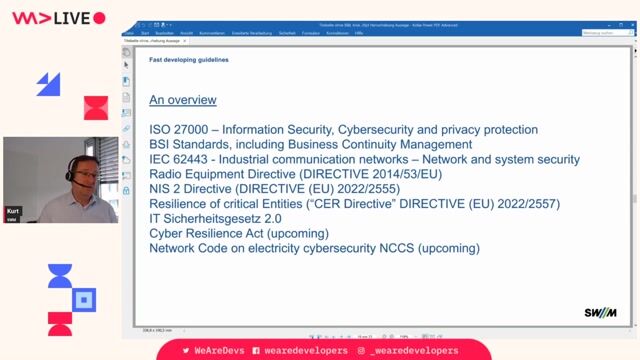
- Assess cloud security posture against frameworks (e.g., CIS, NIST, ISO 27001) and Microsoft benchmarks (Azure Security Benchmark, M365 baseline).
- Define cloud security strategy, target operating model, and roadmap aligned to business and regulatory requirements.
- Develop and maintain cloud security policies, standards, and guardrails for Azure and M365.
Identity and Access Management (IAM)
- Design and implement Microsoft Entra tenant architecture, including identity lifecycle, conditional access, and MFA.
- Implement and tune Conditional Access policies, risk-based access, and device compliance integrations with Intune/Endpoint Manager.
- Deploy and operate Privileged Access Management (PAM), including PIM for Azure and M365 roles, just-in-time access, and break-glass accounts.
- Integrate on-premises identities (hybrid) with secure synchronization and hardening of federation where used.
Platform Security and Hardening (Azure)
- Build secure landing zones using Azure Policy, Blueprints/Bicep/Terraform, and management groups.
- Enforce baseline controls for networking (NSGs, Azure Firewall, Private Link), compute (secure images, patching), and storage (encryption, private endpoints).
- Configure Azure Key Vault for secrets, keys, and certificates management with RBAC and purge protection.
- Implement workload isolation, tagging, and resource locks; manage identity-based access (managed identities).
Threat Protection and Monitoring
- Deploy and tune Microsoft Defender for Cloud, Defender for Cloud Apps (MCAS), Defender for Endpoint, and Defender for Identity.
- Configure Microsoft Sentinel: data connectors, analytics rules, UEBA, watchlists, workbooks, and SOAR playbooks (Logic Apps).
- Develop detection use cases, threat hunting queries (KQL), and incident response runbooks specific to Azure and M365 threats.
- Establish alert triage, escalation paths, and continuous tuning to reduce noise and improve mean time to detect/respond.
Microsoft 365 Security
- Configure and manage Microsoft Purview (Compliance portal) for DLP, information protection labels, data lifecycle, and insider risk.
- Implement Exchange Online, SharePoint, OneDrive, and Teams security baselines, safe links/attachments, and anti-phishing policies.
- Enforce device compliance via Intune, app protection policies, and conditional access for BYOD and corporate devices.
- Secure collaboration and external sharing with sensitivity labels, access reviews, and entitlement management.
Data Protection and Encryption
- Design data classification and labelling strategies with Microsoft Purview; enforce DLP across endpoints, Exchange, SharePoint, and Teams.
- Ensure encryption at rest and in transit, customer-managed keys (CMK), and double encryption where required.
- Implement eDiscovery, legal hold, and audit configurations for regulatory needs., Please be aware that the creation and submission of application documents (e.g. CV, cover letter, case studies, etc.) using AI-powered tools is only permitted to a limited extent.
Our expectations: Application documents must authentically reflect your own qualifications, personality, and motivation.
The use of AI for supportive purposes (e.g. spell-checking, improving wording) is acceptable.
Fully generated application documents created by AI without personal adaptation or review are not permitted.
Under no circumstances may NVISO information, data, or documents be uploaded to or processed by external AI tools.
We reserve the right to exclude applications from the selection and interview process that are clearly created primarily or exclusively by AI and show no recognizable personal input.
The purpose of this policy is to ensure a fair and transparent recruitment process and to obtain an authentic impression of our applicants. If you require alternative methods of application or screening, you must approach the employer directly to request this as Indeed is not responsible for the employer's application process.
Requirements
Do you have experience in Terraform?, Do you have a Bachelor's degree?, * You hold citizenship in one of the 32 NATO member states.
- At least 1 year of experience in information security specific to Azure or Microsoft 365 cloud environments.
- Proven expertise with Microsoft's cloud services, including Entra ID, Microsoft Sentinel, and Microsoft Defender for Cloud, Defender for Endpoint, Defender for Cloud Apps, Defender for Identity, Intune, and/or Purview.
- Experience with cloud security best practices and related frameworks. For example: CIS Benchmarks, Microsoft Cloud Security Benchmark, etc.
- Strong communication, documentation and reporting skills.
- Relevant current Microsoft cloud certifications. For example: AZ-104, SC-900, SC-200, SC-300, SC-401, or AZ-500.
Preferred:
- Bachelor's degree in Computer Science, Cyber Security, Information Security, Engineering, Information Technology, or related studies.
- Experience in consulting.
- Other vendor-agnostic cybersecurity certifications. E.g. SSCP, CompTIA Security+, or equivalent.
- Experience with scripting languages such as PowerShell or Python.
Benefits & conditions
At NVISO, we care. We are committed to offering you a highly competitive remuneration package including financial and non-financial components:
- A training budget of 10.000€ and 10 days every 2 years
- Company car and Belgian fuel card
- Working and learning from the best people in the European cyber security industry. We have multiple SANS Instructors working at NVISO, our staff has presented at popular hacking conferences (BlackHat, BruCON, OWASP, etc) and all of our technical staff can acquire deep technical security certifications (GSE, GXPN, GREM, GCFA, OSCP, etc)
- An entrepreneurial and agile working environment, where you will be challenged, stimulated and supported in driving new initiatives (either through internal innovation or by improving our service offering), without losing sight of having fun!
- Regular team-building and fun events with legendary off-site events once a year. The location of the next team building is one of the most closely guarded secrets at NVISO… We can however disclose that we've visited Lisbon, Dubai, Malta and Lapland over the past few years;
- Our commitment to coach and counsel you and help you grow; each employee receives a personal coach within the team, whose role is to ensure your well-being and helps you grow in your career!
- Flexible working hours, working from home and even the possibility to work from abroad;
- Flex Income Plan
- 32 paid leave days