Penetration Tester
Role details
Job location
Tech stack
Job description
We are seeking a highly skilled Penetration Tester with proven experience in red-team operations, advanced technical compromise, and deep knowledge of modern computing, mobile, and radio-frequency ecosystems. This is a project-to-project contract role, supporting clients who require realistic, technically sophisticated adversary-emulation engagements., * Perform authorised compromise testing against user accounts, cloud identities, email platforms, and online services within defined rules of engagement.
-
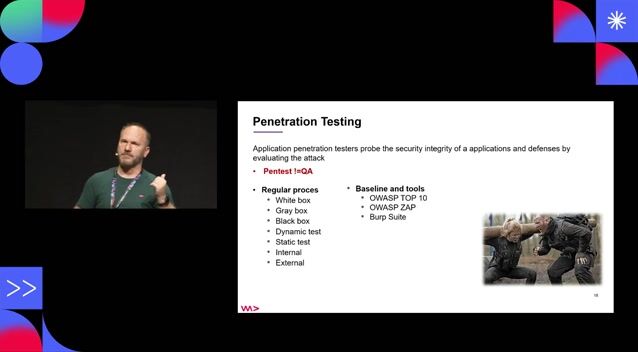
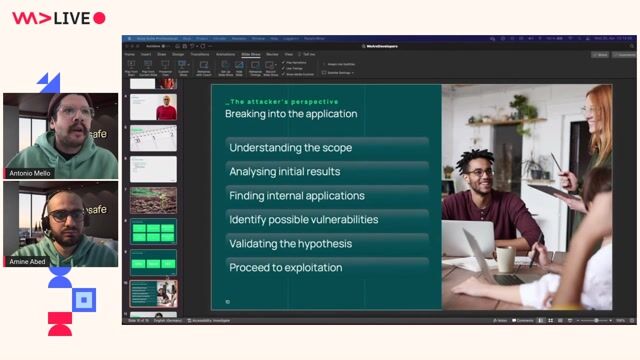
Conduct red-team operations including reconnaissance, initial access, lateral movement, privilege escalation, and data-access simulation.
-
Assess mobile device security, including architecture analysis, application behaviour, and payload deployment.
-
Execute network, cloud, web application, and API penetration tests.
-
Perform RF and SDR-based assessments, including analysis of wireless protocols and device communication security.
-
Develop, adapt, and deploy custom payloads, exploits, and tooling.
-
Produce clear, evidence-driven technical reports and executive summaries.
-
Present findings to technical and non-technical stakeholders.
-
Maintain up-to-date knowledge of attacker TTPs, emerging vulnerabilities, and offensive tooling.
-
Operate strictly within legal and ethical boundaries, following client-approved scope and engagement rules.
Requirements
Do you have experience in iOS?, The role involves conducting authorised attempts to compromise systems, accounts, devices, and infrastructure using whatever attack paths you determine to be most effective within the agreed scope. Engagements may include identity compromise, cloud intrusion, mobile-device exploitation, RF-based assessments, and full red-team operations. You will be expected to operate autonomously, think creatively, and demonstrate a high level of technical depth across multiple domains., * Demonstrated experience in red-team engagements or advanced offensive security roles.
-
Proven ability to compromise systems and identities using a wide range of technical attack paths.
-
Strong understanding of mobile device architecture, including iOS and Android internals.
-
Experience developing and deploying payloads across multiple platforms.
-
Proficiency with SDR, RF analysis, and wireless protocol assessment.
-
Deep knowledge of Linux, including Ubuntu-based environments, system internals, and toolchains.
-
Strong programming and scripting ability in languages such as Python, C/C++, PowerShell, Bash, or similar.
-
Familiarity with offensive frameworks such as Cobalt Strike, Metasploit, Burp Suite, BloodHound, Empire, or equivalents.
-
Excellent communication and reporting skills.
-
Relevant certifications (e.g., OSCP, OSEP, OSCE, CRTO, CREST CRT/CCSAS) are advantageous but not required if experience is demonstrably strong.
Engagement Model
-
Contract / Freelance, project-to-project.
-
Engagements range from short, targeted compromise tests to multi-week red-team operations.
-
Primarily remote, with occasional on-site work depending on project scope., A technically exceptional offensive security professional who can independently identify, design, and execute attack paths across diverse environments. You should be comfortable working with complex systems, emerging technologies, and unconventional vectors, while maintaining the discipline and clarity expected in client-facing consulting work.