Penetration Testing Team Lead
Role details
Job location
Tech stack
Job description
️ Build the Offensive security function from the ground up: define methodologies, reporting standards, and the hiring plan for future team expansion. ️ Recruit, mentor, and develop the team of offensive security engineers, ensuring technical excellence and consistent delivery quality once hired. ️ Perform deep-dive manual penetration testing for complex, high-risk, or business-critical assets, focusing on realistic attack scenarios rather than high-volume "bug-bounty style" findings. ️ Lead and coordinate purple team exercises with the SOC/Blue Team, simulating real-world attacks to validate detection capabilities and tune SIEM/EDR rules. ️ Collaborate closely with the Application Security Team to validate vulnerabilities and guide effective remediation strategies. ️ Translate offensive findings into actionable threat intelligence, TTPs, and recommendations to enhance detection and threat hunting. ️ Act as a subject matter expert in security architecture discussions, secure design reviews, and security code reviews. ️ Stay current with emerging attack techniques, tools, and security trends, and ensure knowledge is shared within the engineering teams.
Areas of Ownership: ️ 0-to-1 establishment of the offensive security capabilities and team roadmap. ️ End-to-end ownership of penetration testing execution, quality, and reporting. ️ Identification of critical attack paths that threaten the company's core business products. ️ Delivery of TTPs and threat-hunting insights for purple team initiatives. ️ Effective cross-team collaboration with Application Security, Security Operations, and Engineering.
Requirements
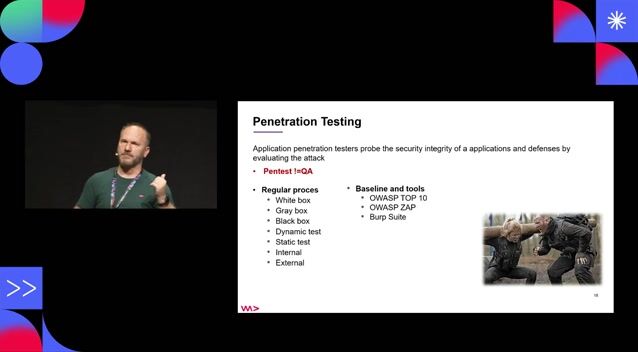
️ 5+ years of hands-on experience in Penetration Testing, including web, mobile, API, and cloud environments (AWS, Azure, GCP). ️ Experience building offensive security processes, methodologies, or tools from scratch. ️ Strong "playing coach" mindset: willingness to remain highly hands-on (70-80%) while setting up the function. ️ Deep understanding of penetration testing methodologies and frameworks (OWASP Top 10, SANS Top 25). ️ Demonstrated experience contributing to purple team exercises and working closely with SOC to improve detection logic. ️ Strong hands-on experience with industry-standard tools (Burp Suite Pro, Metasploit, Nmap, etc.) and ability to develop custom automation (Python, Go, PowerShell, Bash). ️ Solid knowledge of network protocols (TCP/IP, HTTP/S, DNS), operating systems (Linux, Windows), and cloud-native architectures (Docker, Kubernetes). ️ Excellent communication skills, with the ability to clearly present critical business risks to both technical and non-technical stakeholders.
Nice to Have: ️ Advanced certifications such as OSCP, OSCE, OSWE, CRTP, or SANS GIAC. ️ Experience in fast-growing companies (Gaming/Fintech) with exposure to industry-specific security challenges.
Benefits & conditions
Opportunity to develop language skills, with partial compensation for the cost of Spanish classes (for localisation purposes). ️ Relocation package (tickets/2 weeks accommodation, and visa support). Global coverage health insurance. Time for proper rest, with 23 working days of annual vacation and an additional 6 paid sick days. Competitive remuneration level with annual review. Teambuilding activities.