Penetration Tester
Role details
Job location
Tech stack
Job description
The Penetration Tester supports operational test and evaluation activities by conducting cybersecurity assessments against operational systems. This role assists in the development of cyber test plans, execution of cyber tests, and reporting of results across laboratory, cyber range, and live environments. Testing may involve physical, virtualized, or cloud-based systems.
The position leverages authorized tools, analytic techniques, and ethical hacking methodologies to assess networks and systems under test in support of cyber operational test and evaluation missions. Work is performed under the supervision of a Cyber Operations Officer., * Develop, execute, and report on cyber test plans supporting operational and developmental test events.
- Review and become proficient in cyber test and evaluation concepts of operations, SOPs, policies, and guidance.
- Participate in the development and maintenance of SOPs and documentation supporting authorization and compliance requirements.
- Research, prioritize, and submit operational requirements for acquisition of cyber tools and capabilities.
- Develop and execute tactics, techniques, and procedures (TTPs) for penetration testing and Red Team operations.
- Research adversary cyber actors, including their TTPs, organizational structures, capabilities, personas, and environments, and integrate findings into test planning and execution.
- Support cyber test planning activities, including:
- Open-source research and system-under-test documentation reviews to identify mission context, architecture, interfaces, attack surfaces, and threat vectors.
- Participation in checkpoint meetings and planning reviews.
- Development and feasibility review of test plan objectives.
- Participation in test planning site visits.
- Support test preparation activities, including:
- Pre-test coordination visits and briefing support.
- Red Team test plan reviews.
- Maintaining test reference libraries with relevant system technical information.
- Organizing and supporting research presentations for advanced capability development.
- Preparing government-furnished test assets.
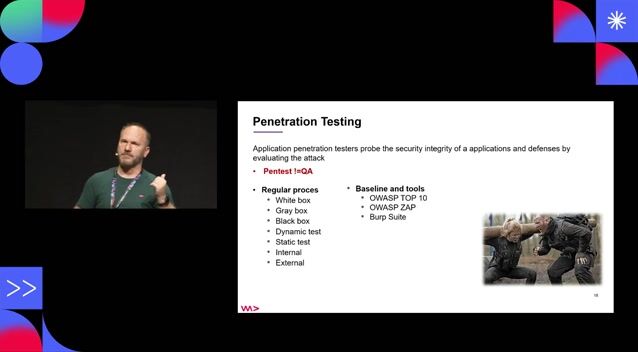
- Execute test events such as cooperative vulnerability penetration assessments, adversarial assessments, and cyber tabletop exercises.
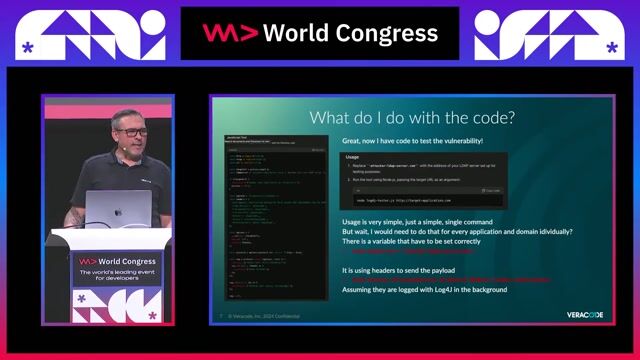
- Utilize approved commercial and open-source cyber assessment tools to accomplish test objectives.
- Conduct testing independently while ensuring safety, procedural compliance, and adherence to deconfliction requirements.
- Validate and verify collected data for accuracy and completeness.
- Participate in post-test activities, including documentation of deficiencies, risks, and lessons learned.
- Support capture-the-flag events, cyber off-sites, and external technical exchanges; develop materials supporting these efforts.
- Attend required meetings in support of operational test and evaluation.
- Generate and update documentation to maintain authorization compliance.
- Process exfiltrated data for analysis and dissemination.
- Test and evaluate locally developed tools for operational use and implementation.
Requirements
- Minimum 3 years' experience performing a combination of penetration testing, red teaming, or exploitation development.
- Minimum 3 years' experience with proficiency in leading red team operators in penetration testing and/or red teaming to accomplish assigned test objectives.
- Offensive Security Certified Professional (OSCP), OSCE, GX-PT, GXPM, PNPT, or HTB CPTS required.
- Proficient in multiple offensive tools, including:
- Metasploit
- Cobalt Strike
- Core Impact
- Burp Suite
- Nessus
- SharpHound/BloodHound
- Ability to validate functionality and safety of offensive tools (e.g., exploits) using source code review and document the results.
- Ability to detect malicious activity of a program using dynamic analysis techniques and document the results.
- Ability to independently conduct penetration testing and/or red teaming to accomplish assigned test objectives.
- Skill in assessing current tools to identify needed improvements.
- Skill in knowledge management, including technical documentation techniques (e.g., wiki pages).
- Knowledge of current software and methodologies for active defense and system hardening.
- Knowledge of encryption algorithms and cyber capabilities/tools (e.g., Transport Layer Security, Pretty Good Privacy).
- Knowledge of evasion strategies and techniques.
- Knowledge of forensic implications of operating system structure and operations.
- Knowledge of host-based security products and how they affect exploitation and vulnerability.
- Knowledge of network administration.
- Knowledge of network construction and topology.
- Knowledge of security hardware and software options, including network artifacts they generate and their effects on exploitation.
- Knowledge of security implications of software configurations.
- Knowledge of the fundamentals of digital forensics to extract actionable intelligence.
- Knowledge of cryptologic capabilities, limitations, and contributions to cyber operations.
- Knowledge of Unix/Linux and Windows operating system structures and internals (e.g., process management, directory structure, installed applications).
- Knowledge of network collection procedures, including decryption capabilities, tools, techniques, and procedures.
- Ability to process exfiltrated data for analysis and/or dissemination to customers.
- Ability to test and evaluate locally developed tools for operational use.
- Skill in testing and evaluating tools for implementation.
- Proficient in Microsoft Office Suite, including Teams or similar workplace chat and videoconferencing tools.
- Excellent written and verbal communication skills.