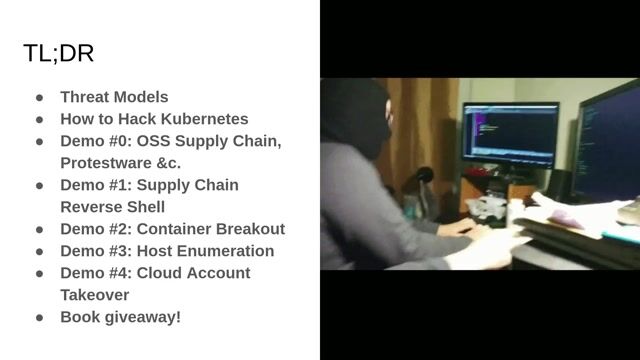
Threat Intelligence
Role details
Job location
Tech stack
Job description
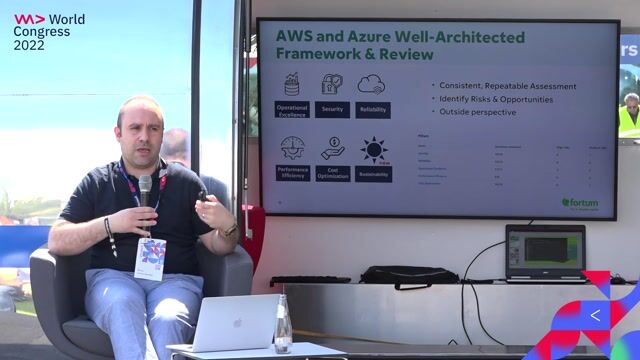
Title: Principal Cybersecurity Detection Engineer AI-Driven Threats Location: Vienna, VA, Pensacola, FL, Winchester, VA (HYBRID) Duration: Initial 6 month duration with possible extensions Work Requirements: , Holders or Authorized to Work in the U.S. Principal Cybersecurity Detection Engineer AI-Driven Threats The Principal Cybersecurity Detection Engineer AI Driven Threats is a senior individual contributor responsible for advancing the effectiveness and maturity of the Cyber Security Operations Center (CSOC). This role designs, operationalizes, and scales high confidence detection capabilities to address AI enabled threats and related emerging attack techniques. The position combines deep, hands on detection engineering expertise with applied knowledge of AI security and adversarial techniques. As a principal level individual contributor, this role drives the practical application of AI and emerging technologies within security operations, ensuring measurable improvements in detection fidelity, incident response outcomes, and analyst efficiency., AI & Emerging Threat Detection Serve as the senior technical subject matter expert for AI focused threat detection within the CSOC. Design, develop, deploy, and maintain advanced detection content across SIEM and security platforms to identify AI enabled and emerging attack techniques. Engineer high confidence detections using complex query languages and techniques (e.g., SPL, KQL, regex, YARA, macros, lookups) across on premises, hybrid, and cloud environments. Continuously evaluate detection coverage and fidelity, tuning or retiring content as adversary tactics, data sources, and operational needs evolve. Research emerging AI and advanced technology threats (e.g., prompt injection, model poisoning, adversarial AI, data exposure) and translate them into actionable detection strategies. Align detection use cases to industry frameworks such as MITRE ATT&CK, MITRE ATLAS, and NIST CSF. Partner with threat intelligence, detection engineering, threat hunting, red team, and architecture teams to proactively strengthen detection capabilities. Support proofs of concept and pilots that apply AI to detection engineering and SOC operations, ensuring solutions deliver measurable operational value. Mentor and guide senior detection engineers and analysts on AI threat concepts and advanced detection strategies. Communicate complex technical findings clearly to technical teams, leadership, and executive stakeholders.
Requirements
7+ years of experience in cybersecurity operations, detection engineering, or SIEM engineering in a senior individual contributor role. Advanced expertise in detection engineering across the full content lifecycle (design, testing, deployment, tuning, and decommissioning). Hands on experience applying AI or machine learning capabilities within SOC or detection workflows. Familiarity with AI security frameworks (e.g., MITRE ATLAS, OWASP AI Security). Advanced proficiency with SIEM query languages and multi source telemetry across on prem, cloud (IaaS/PaaS/SaaS), and hybrid environments. Strong understanding of adversary TTPs, including emerging AI enabled threats. Demonstrated ability to analyze large scale log and telemetry datasets to identify threats and detection gaps. Strong communication skills, with the ability to present complex technical concepts to both technical and non technical audiences., Experience leading or contributing to AI focused SOC pilots, automation initiatives, or advanced detection programs. Relevant certifications (e.g., CISSP, CySA+, CASP+, CCSP) or comparable credentials. Bachelor's degree in Cybersecurity, Computer Science, Engineering, or a related field.