L1 SOC Analyst - 100% Remote
Role details
Job location
Tech stack
Job description
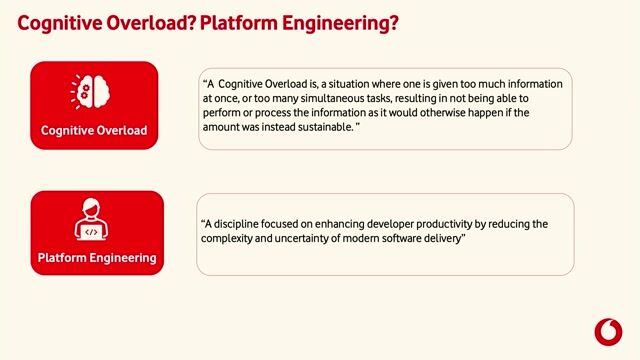
- Analytical thinking abilities, in addition to adhering to playbooks, as certain cases may have variations where standard steps may not apply.
Main and commonly use tools are:
- Palo Alto XSOAR - since this is the CDC-like where we get/handle all of our s
- Palo Alto XDR - Performing search queries to determine if user's device is really compromised or false positive
- ProofPoint
- Big bulk of the incidents came from proofpoint, knowing where to look for information can greatly speed up the triaging process.
- Microsoft
- Useful to gather critical information that could determine if the incident is false positive (e.g. User's connection status)
- ServiceNow (SNOW)
- Analysts are required to handle request from users but this platform can be a very useful tool which can close incidents as false positive without the need for further investigations (E.g. Approval had already been given to perform some tasks when user had previously requested it in Servicenow)
Requirements
Do you have experience in Splunk?, siem,incident response,python,qradar,threat intelligence,splunk
Benefits & conditions
`Retribución Flexible´ Program: (Meals, Kinder Garden, Transport, online English lessons, Health Care Plan…)
Free access to several training platforms
Professional stability and career plans
UST also, compensates referrals from which you could benefit when you refer professionals.
The option to pick between 12 or 14 payments along the year.
Real Work Life Balance measures (flexibility, WFH or remote work policy, compacted hours during summertime…)
UST Club Platform discounts and gym Access discounts