Information Security Incident Response Analyst
Role details
Job location
Tech stack
Job description
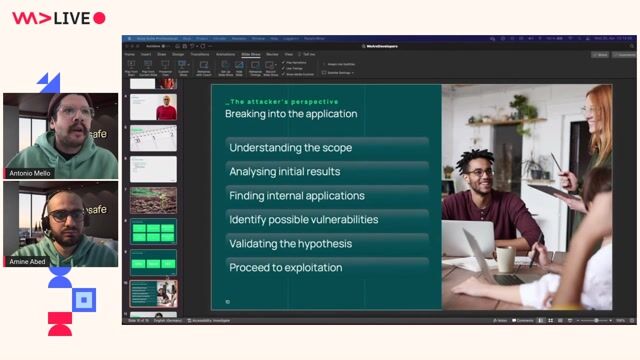
The Information Security Incident Response Analyst supports clients during security incidents by performing technical investigations, analyzing digital forensic evidence, and assisting with containment and remediation activities. This role focuses on identifying indicators of compromise, reconstructing attacker activity, and communicating clear, actionable findings.
The analyst works as part of a global DFIR team, handling a variety of incident types across diverse environments. They contribute to process improvements, maintain strong client communication, and continue building advanced DFIR skills through hands-on investigations and internal project work., * Investigates security incidents by performing host, disk, memory, network, and cloud forensic analysis under established processes and guidance.
- Analyzes artifacts across Windows, Linux, and macOS systems, helping reconstruct timelines and determine root cause.
- Supports clients through containment and recovery efforts by providing technical recommendations and clear communication.
- Participates in the team's on-call rotation for urgent incident response needs.
- Completes internal and client tasks such as tabletop exercises, IR readiness assessments, basic forensic reviews, and environment hardening support.
- Identifies observable gaps and risks within client environments and recommends improvements to strengthen security posture.
- Produces accurate documentation-including investigation notes, status updates, and final reports.
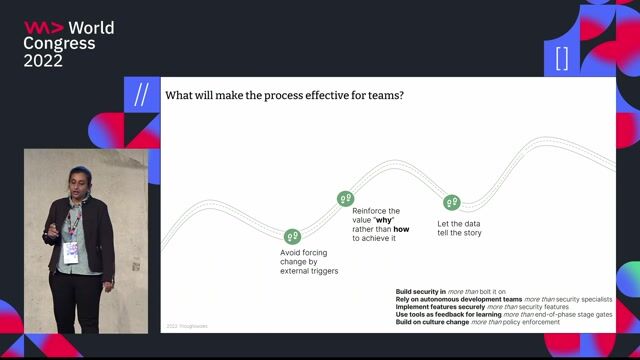
- Collaborates with global DFIR and other teams and stays current on threats, attacker techniques, and emerging forensic tools.
Requirements
Do you have experience in macOS?, Do you have a Bachelor's degree?, * Solid understanding of digital forensics fundamentals, including host-based analysis across major operating systems.
- Working knowledge of network forensics, cloud log analysis (e.g., Azure, AWS, GCP), and common forensic tools.
- Ability to clearly communicate technical findings to both technical and non-technical audiences.
- Strong analytical and problem-solving skills, especially during time-sensitive investigations.
- Motivated to continuously learn deeper DFIR techniques and methodologies., * Proven experience in incident response and digital forensics, with capability in host-based, image, and log analysis.
- Experience using SIEM, EDR, IDS/IPS, and other security tools to triage, investigate, and respond to incidents.
- Ability to perform network analysis using tools such as Wireshark, tcpdump, and other tools.
- Experience in cybersecurity operations, consulting, DFIR services, or related technical security roles., * Bachelor's degree or equivalent experience in Information Technology, Computer Science, Cybersecurity, or a related discipline (preferred).
- Relevant cybersecurity certifications such as:
- SANS GIAC Security Essentials (GSEC) or equivalent preferred.
- SANS GIAC Certified Intrusion Analyst (GCIA) or equivalent preferred.
- SANS GIAC Certified Incident Handler (GCIH) or equivalent preferred.
- Additional DFIR-related certifications are considered a plus.
Additional UK-Specific Role Requirements
UK Security Clearance
- Active UK Security Clearance is required to deliver services within sensitive or regulated client environments.
Operational Technology (OT) Incident Response & Digital Forensics
- Background and hands-on experience in OT environments.
- Experience investigating ICS/SCADA systems and industrial sectors such as manufacturing, energy, utilities, or critical infrastructure.
- Ability to collect and analyze OT forensic artifacts, interpret OT protocols and system behavior, and assess the impact of cyber incidents on physical processes.
Certifications
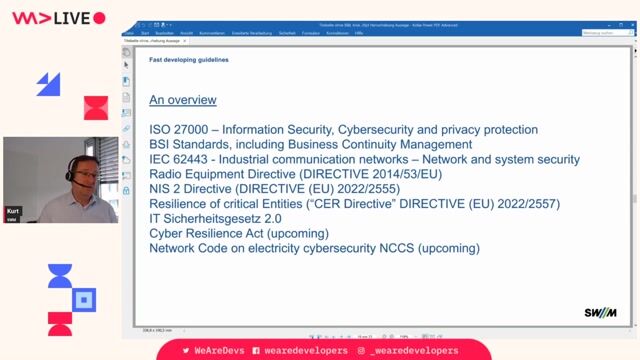
- SANS OT/ICS certifications such as GICSP or GRID, IEC 62443 or equivalent required.