Incident Manager III
Role details
Job location
Tech stack
Job description
-
Supporting the management of cyber incidents through the incident response lifecycle.
-
Creating and maintaining routine reporting of cyber incidents in official systems of record, to include case management systems and ticketing.
-
Coordinating with internal and external customers, partners, and stakeholders.
-
Ingesting, validating, and evaluating information to determine optimal courses of action, to include providing response support to requesting entities.
-
Updating and tracking cases and tickets with accuracy, timeliness, reliability, and consistency.
-
Drafting summaries of ongoing operations and be able to provide oral presentations for various levels of leadership.
-
Maintaining knowledge objects in system of record consistently and professionally.
-
Supporting teams that apply risk management and protocols to evaluate risks and prioritize responses based on national security strategies (NCISS).
-
Supporting teams conducting threat and vulnerability management to recognize and categorize types of vulnerabilities, threat actors, and different operational threat environments, and associated attacks (MITRE ATT&CK framework).
-
Support teams performing network security monitoring and/or security operations analysis, system administration, operating system hardening, cyber hygiene techniques, and cybersecurity defense policies, procedures, and regulations.
Other:
-
Familiarity with different operational threat environments (e.g., first generation [script kiddies], second generation [non nation-state sponsored], and third generation [nation-state sponsored])
-
Familiarity with system and application security threats and vulnerabilities (e.g., buffer overflow, mobile code, cross-site scripting, PL/SQL and injections, race conditions, covert channel, replay, return- oriented attacks, and malicious code)
-
Familiarity with of basic operating system hardening techniques, Computer Network Defense policies, procedures, and regulations
Requirements
-
U.S. Citizenship
-
Must have an active TS/SCI clearance
-
Must be able to obtain DHS Suitability
-
5+ years of directly relevant experience in cyber incident management or cybersecurity operations
-
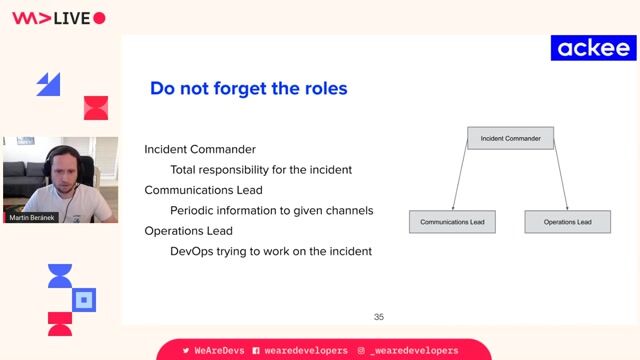
Knowledge of incident response and handling methodologies
-
Having close familiarity with NIST 800-62 (latest revision), and FISMA standards as they pertain to reporting incidents.
-
Knowledge of the NCCIC National Cyber Incident Scoring System to be able to prioritize triaging of incident
-
Knowledge of general attack stages (e.g., foot printing and scanning, enumeration, gaining access, escalation of privileges, maintaining access, network exploitation, covering tracks, etc.)
-
Skill in recognizing and categorizing types of vulnerabilities and associated attacks
-
Knowledge of different operational threat environments (e.g., first generation [script kiddies], second generation [non nation-state sponsored], and third generation [nation-state sponsored])
-
Knowledge of system and application security threats and vulnerabilities (e.g., buffer overflow, mobile code, cross-site scripting, PL/SQL and injections, race conditions, covert channel, replay, return- oriented attacks, and malicious code)
-
Excellent oral and written communication skills
-
BS Incident Management, Operations Management, Cybersecurity or related degree. HS Diploma with 7-9 incident management or cyber security experience